Introduction
Today in the emerging world of innovation, everything is done with help of technology. Every person regardless of age are come in influence of technical device in terms of products they purchase. With the emergence of online services, people can easily sell or purchase products of national and international companies. Similarly, in the field of communication, technology has developed so far. It makes life of people more easy by which they can make transform information and convey messages in faster manner.
Computer system is a device that can be instructed to carry out operations automatically through computer programming (Hsiao, Kerr and Madnick, 2014). Modern computers have at least one processing element. It allows users to store large amount of data for longer period more safely. Such type of technology is flexible also because it can process any task by loading a programme more accessibly. With development of technology, computer systems are becoming more innovative. It includes a wide range of "smart" devices, such as televisions, smart phones and tiny devices. Mobile phones not only include Internet and or private data networks, but also other wireless too. It involves Hot-Spot, Blue-tooth, Wi-Fi and so on. But all these internet and wireless network impact on security of data. It creates various security issues like data leakage, broken cryptography, hacking and more.
TASK
With rapid development of technology, innovation in products and services are done in regular manner. It gives various opportunities to human beings in doing their daily routine works more easily. It includes computers, mobile phones, vehicles, internet applications and more. Among these smart phones, tablets, internet applications and other communication devices are considered as best technologies which connects whole world. A person whether belongs to metropolitan or a remote area cannot imagine their life without such device. It enables them to make interaction with rest of the world, get knowledge about news, access to internet services via 3G/4G or Wi-Fi and conduct various activities of every aspect of their lives. Some other benefits are e-mail, web browsing, maps and navigation, net-surfing, net-banking for managing our bank accounts and making payments, etc. Phones are also give opportunity to address books and contact lists, take photographs, videos, make diaries, notes and so on. Further, usage of mobile or smart phones is classified as per ordinary and business purpose. For example: A normal person use such devices to make phone or video calls, internet surfing, playing games online shopping, making order for pizza etc. While people belong to organisation use smart phones for business purpose i.e. online meetings, paying tax bill, and more. Thus, to do business operations, companies use specific code and software which help in preventing data and information from criminal or illegal activities. But in case of ordinary people using net banking, e-payment, internet access, involve their personal data which may be of use to those with criminal intent. It has observed that mostly users or common people do not aware about criminal activities and how to protect their personal data from illegal access.
In this regard, some major threats agents and how such issues are recognised, given as below:
Threat agents
With development of technology, mobile phones have become more advance. It includes a wide application of internet services, high-digital pixels, sharp features and more. But as far as internet services developed in mobile phones, threats agents also rise. A threat in this regard, can be defined as a newly discovered incident which has potential to create harm to mobile system. In general, intentional threats in computer system and smart phones include malware, adware and spyware. Along with this, viruses and worms are also considered as threats as also they have potential to harm system and functions (Computer Networking Issues, 2018). All these agents create various issues as mentioned below:-
(a) Data Leakage
It refers to unintentional data leakage in which an application takes your personal data from your mobile when you sign in. The main reason for data leakage is all risk ware applications that takes sweeping permissions from users. To prevent yourself from these technical hazards don't give access of your personal data to applications until they insist you to do that. It is illegal and unlawful transfer of information from computer to outside world. There are many types of data leakage and this problem can be attack through externally and internally. There is a need to implement protective regulatory measures in all areas to prevent data leakage.
(b) Unsecured Wi-Fi
All free wireless networks are mostly unsecured because technology experts can easily hack you to get your personal data. To be safe from this security issue don't give access to your personal information like bank account information while using wireless networks.
(c) Network Spoofing
It is a type of threat in which hackers establish fake Wi-Fi access points in public locations like airports, coffee shops and shopping malls and force users to make accounts to take their secure information. So to prevent public from this threat, they have provided with unique passwords which helps in reading messages by authorisers only.
(d) Spyware
Spyware is generally installed by spouses, employers, team members to keep detailed record of whereabouts and use patterns. To be safe from this threat use an appropriate antivirus to prohibits these programmes in accessing personal data.
(e) Broken Cryptography
This threat occurs when a developer uses weak algorithms or strong algorithms in its encryption process without proper implementation (Mendenhall, Sincich and Boudreau, 2016). Through this any hacker can crack and get passwords of user to gain access.
So these possible threats are considered as technical hazards for mobile users which can easily harm mobile performance of a user and can get access to their personal information.
Threat response
In terms of computer security which is also known as cyber or IT security, is defined as protection of information systems from theft or damages. It also prevents system from damage and disruption of hardware, software or other information. For this purpose, it controls physical access to hardware, protecting against harm which may generate due to network access, malpractice by operators, data and code injection and more. Therefore, to prevent system from all these security issues and threats which damage hardware and software are:
TCP/IP Protocol: This tool specifies how any data is exchanged over internet by giving end-to-end communications (Peltier, 2016). It has developed to secure tablets, phones and other communication devices from theft and damages. It makes network more reliable as well as have ability to recover the lost data automatically.
Encryption: In cryptography, it is defined as process of encoding a data or information in such manner that only authorised person can access it. Encryption doesn't prevent interference but it actually contradicts the intelligible information to would-be interceptor.
Decryption: It is a process of using encrypted data or information which further converted back into readable text by users. Therefore, it also prevent information from theft as to read such data, a person needs to enter a decryption pass-code.
Cryptography
It is a process of transforming a normal text into a dense text and vice-versa. It is a technology that is used to eradicate theft or alteration of a particular text which is readable to a particular person for whom it is intended. It is introduced to solve all social security related issues which are growing rapidly in technological environment (Ahmed and Hossain, 2014). It is important for IT firm to use cryptography approaches to solve breaches and attacks arises in technology.
Types of Cryptography
(a) Private key Cryptography
It is also known as same key cryptography in which a same key is applied to encrypt a cryptography text from both receiver and the sender. In this receiver and sender knows a secret key for encrypting a plain text that's why it is known as private key cryptography.
(b) Public key Cryptography
It is also known as different key cryptography in which receiver and a sender uses a different key to encrypt a plain text and vice versa. In this a sender has a key for encryption and receiver has a key for decrypting a received text.
(c) Hash Cryptography
In hash cryptography key is not play a crucial role but the text is incorporated by both parties through hash. In this sender uses a hash function on a plain text to encrypt and receiver also do the same to decrypt a text.
Various Approaches of Cryptography
(a) Trusted Third Party Cryptography
It is also known as trusted cryptography approach. In this an administrator hires third party for security issues related to the network. In this third party can send or receive messages freely without thinking of security issues (Comer, 2018). All communications in this approach is undertaken by a third party and it is also responsible for authenticity related issues.
(b) Peer to Peer cryptography
In this an administrator never uses third party to undertake security related issues unless their main focus is on cryptography algorithms. There are two stages in this approach, in first stage stations exchange keys and in second stage sending and receiving of encrypted messages take place. This approach helps in securing communication happens between two work stations.
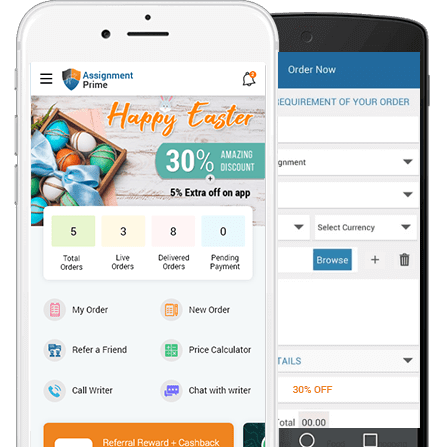
Assignment Prime is an online assignment writing service provider which caters the academic need of students.
Get Best Pricing Quotes Free Samples Email : help@assignmentprime.com Order NowApplications of Cryptography
(a) Secure Connection
Cryptography helps in building secure connection between sender and a receiver while encrypting and decrypting a plain into crypto text. It is mainly used when an administrator is communicating with a client program and a server. In order to make mobile system and internet more secure, now, all communication protocols have included an application of encryption. In this regard, best example is web encryption, because here users can select an encrypted version of a website (Sun and et. al., 2014). For this purpose, they can switch latest versions like HTTP or HTTPS in URL. Mostly communication or mobile manufacturing companies use the encrypted form as per default where they see any type of visit to Google, Microsoft Office 365, Facebook and other websites. Now, installing HTTPS versions in recent browsers, users can get extra information like a padlock. For this purpose, for net surfing or before entering a password, users are required to ensure about HTTPS version in their mobile phones.
(b) End to end encryption
It is an application of cryptography that is used to secure email conversation between encrypting and decrypting parties. It also helps in building truly secure systems between a sender and a receiver. In general, e-mail is considered as single area where any kind of encryption is not used in wide manner. The reason behind this is that when information by email application moves from one server to another then it is encrypted automatically. But on mail server, authorised administrators can read it. Therefore, there are other options available for implementing end-to-end encryption. For secure messaging systems, now many applications are launched where only sender and receiver have access to read messages of each other. It includes Whatspp, Skype and more, where encryption has already been built.
(c) Storing Data
Today every person stores personal data in a mobile phone for storage and keeps in memory. So, this application of cryptography helps people to secure their personal information in their mobile phones more securely (Savulescu, 2014). It will help an administrator to eradicate breaches arises in storing personal data. Furthermore, one of the most important beneficial parts of cryptography is storing passwords more securely. Sometimes, it seems to very risky for users to store passwords in device in an accessible or confidential manner. If they stored password in text-form in their system than under security issues it seems to be legitimate or malicious. Hackers can read password intentionally. In this regard, encryption helps in storing passwords more securely. They will allow to store encrypted password as well as can decrypt also.
(d) Confidentiality
It is an application of cryptography that ensures that a data should not be disclosed to unauthorised people. The confidential data can only be readable by authorised person who have a permission to read the data.
IT Security in terms of risks, threats and vulnerability
In today’s technology world, data and protecting the information are considered as most critical aspects for every person and organization. In order to deal with data security issues which have potentially to impact on systems and business, it is necessary to understand the concept of three main aspects, that are Threat, Vulnerability and Risk. These technical terms have different-different implications and affects but somehow, they are interrelated also.
Threat can be defined as newly discovered incident which has potential to adversely affect mobile or computer system (Perlman, Kaufman and Speciner, 2016). In general, threats can be classified into further three main components– natural, unintentional and intentional. Here, natural threats are caused by sudden effects like tornado, earthquake and more. While unintentional threat happens when a person access wrong data and use internet or mobile applications in unethical way. Apart from this, intentional threats are caused when someone attempts to access data of others for criminal activities. It includes malware, spyware, adware actions which put people in many troubles. Along with this, viruses and worms are also considered as type of threats, as they also have potential to harm personal data by exposing it to an automated cyber attack.
Vulnerability refers to weak point of an asset which can be exploited by criminal or terrorists. This type of security issues leak personal data and allow attackers to exploit common people or organisations. It generally happens when a person download internet applications and create account on the same by a particular password, after a while they forgot to change password or shut down application or logout. This would lead to develop both kind of intentional and unintentional threats (Bodnar and Hopwood, 2012) (Baase, 2012). Furthermore, vulnerabilities are usually exploited by automated attackers instead of third person. So, when downloading an application, it is essential to check for what purpose it has been used and should timely change the password to prevent system from attackers and vulnerabilities.
Risk may be stated as potential to damage a system or personal to leak personal data when a vulnerability exploited by a threat. In other terms, it can be defined as state when threat and vulnerability both causes simultaneously. It leads to cause financial loss, privacy leakage, illegal and fraudulent activities as well as can create loss of life also.
Critical evaluation on notable security issues in IT
Today digital technology has become a necessary part of everyone's life. It makes work of people more easy and even faster too. In addition to this, technologies like information security is generally need in terms of- Confidentiality; Integrity and Availability. Here confidentiality can be defined as process to control who will get access to read a particular information. While integrity reflects assurance that any data will change only in authorised and specified manner. Similarly, availability makes sure that authorised users can get continued access for reading and using information. According to opinion of Kim and Solomon (2016) it has examined that for national defence system, government concern on ensuring to get confidentiality of private information. While common people are concerned more on funds transfer system which require strong integrity controls. Therefore, requirement for security system will vary with different-different purposes. Some major issues related to information technology are mentioned as below:-
Technical Issues of IT Security: IT system has become a backbone of every organisation without which they cannot operate their business in desired manner. It serves various benefits for stabilizing the working environment. Therefore, this kind of technology also known as vulnerable systems which pose various risk to companies, individuals as well as all types of modern infrastructure. From a technical point of view, there are various types of risks includes within computer or IT systems that are- protocol proxy systems, risks to firewalls, micro fraud schemes, weaknesses of intrusion detection systems, botnet-developments and more.
Individual Victimization and Damages: With development of technologies and rapid use of internet services for personal and professional purpose, cybercrime issues have occurred at fast rate. To overcome from this issue organizations and knowledgeable people install various crime alert system within their device (Liao and et. al., 2013). But in context with ordinary people, they are not much aware that they can become victims of computer crime. Even if when individual are victimized then they do not make reports to regulatory bodies too. Due to an-awareness about whom to report or get fear of the same. Therefore, this section involves risk like extent of victimization by cyber crime, fraudulent activities etc.
Future Developments: Botnets and phishing scams which are considered as fraudulent attempts to get sensitive information like usernames, passwords, details of credit card etc. are some well-known threats which affect cyber security for future development as well. Along with this, other threats or security issues for the same are dangers to supply chains and critical infrastructure, cyber terrorism, online transfer and more.
Cultural, Sociological, Political Implications and Control Issues: This phenomena of cybercrime reflects some major aspects of security implications. It includes usage of Internet in disguise manner like malware, hacking of security measures and so on. When internet and social media are used inappropriate manner then it leads to cause possibilities of various illegal and criminal activities (Levy, 2014). Therefore, societies are must aware of such fraudulent activities which may cause various issues. Furthermore, for a successful fight against such cyber crime and their repercussions, it is necessary for people to aware about phenomena, extent as well as possible future threats. In this regard, with support of IT department, people can take necessary actions against computer or cyber crime. It includes technical instruments, national and international legal techniques and more, which helps in fight against such criminal activities.
Legal, Ethical and Social issues in a secure system
Ethics can be defined as set of rules which guide people what is right and wrong. In management information system, ethics refers to protect and prevent individuals from social or cyber crime. In context with organisation, IT systems have made their businesses most successfully (Schumacher and et. al., 2013). It includes Facebook, Twitter, Google and more, are such applications of IT which helps in connecting world with each other. But any kind of improper use of Internet application can create various problems. It includes leakage of private information, cyber attacks etc. In general, there are some types of social and ethical issues viz. Cyber Crime, Information System Security and ICT Policy.
Cyber Crime
It is a type of crime that is committed with the use of information technology. The rapid increase in a growth of mobile users also contributed in growth of cyber crimes. There are four types of cyber crimes:
Identity theft: In this a criminal get access to an individual's personal information through malfunctions by using someone else's identity. It includes crimes such as, social security numbers, credit and debit card information, passport numbers etc. After accessing the information one can easily make payments online (Stallings and Paul, 2012).. This type of crimes is easy to initiate because most of the peoples didn't have an appropriate information and they easily fall on their traps.
Copyright Infringements: It refers to unauthorised use of copyrighted materials such as video, software, audio etc. From various websites like pirate bay you can easily download copyrighted software like adobe indesign, photoshop which are not officially free for use.
Click Fraud: It is generally done by using automatic software that makes the clicks. It occurs when an individual clicks this type of links with a no intention of knowing what's gonna happen after the click.
Hacking: It is generally done by a criminal to get unauthorised access to a particular system with a motive to steal sensitive information. It is also used to deface a particular website by changing its visual appearances it is also known as electronic graffiti.
Information communication Policy
It refers to set of guidelines which states how individuals and organization should use internet and other applications of IT appropriately. ICT policies mostly include certain guidelines that are:-
- Buy and proper usage of hardware equipment as well as dispose the same adequately.
- Must use licensed software only and individuals should ensure that they used latest version of software.
- Steps to create passwords and access to change the same by authorized users only.
Legal issues in a secure system
(a) Privacy
Privacy is major issue in a secure systems which means when someone from unintended source can get access to your personal information with a motive of stealing your sensitive information (Taylor, Fritsch and Liederbach, 2014).
(b) Digital Ownerships
In today's time intellectual property of an individual is very hard to control because through digital medium information flow has became easier. It is a layer of internet of things which enables us to gain control on gigabytes data.
(c) Secure Liability
Various security systems in digital markets are established to protect important information and assets of an individual user. So it is essential for IT professional to build a secure system which effective and ethical at the same time.
Risk Management Analysis
One of the most crucial security challenges that people and organisations are facing today is the carrier networks which leak data and personal information. This would give advantage to terrorist organizations, hackers and other criminals to exploit them in large manner. To overcome from security issue like cyber crimes activities, data leakage, piracy hacking and so on it is important to provide privacy and legal securities to society. With help of this they can protect their privacy. Various laws have been made for unreasonable search engines. Government are balancing need for safety of public against need to maintain American values of justice and freedom. There has to be a climate where proper security concern leads to increase in cost of performing business (Kizza, 2013).
Constitutional rights those are related to individuals and companies government agencies have to examine and expanding their powers in protecting societies. Establishment of well developed security environment is very important and proper steps are required to quantify and identified. Similarly, development of legal or ethical policies has to be made. There has to be effective examination of policies or procedures so that organisation can protect their valuable property by not violating laws of civil rights. There has to be a sense of security safety in order to hamper terrorist events. To secure and prevent cybercrimes people need to be careful and use well measure securities. Governments must have to implement proper safety measure to avoid any kind of unethical activities. On large organisations and enterprises where business is connected on their computers, one problem affects everyone on network. Despite having profit of using networks there are many securities issues which includes loss of data, security breaches and malicious attacks and hacking or viruses issues. It is important to take measures and implement suitable measures to decrease network vulnerability to unauthorized damage.
Conclusion
It has concluded from this report that today with development of technology, issues related to security also occurred more rapidly. Work of every people and each organisation are totally depended on technology to achieve success. But having not proper knowledge about how to use such techniques, put them in trouble also. It creates various various kind of security issues like threats, risks and vulnerabilities. In context with common people, they don't much have appropriate knowledge about such problems therefore, it leads to cause financial loss, data leakage, piracy and more. Therefore, to overcome from such situations public and government co-operate each other to fight against criminal and cyber attacks.
Reference
- Taylor, R. W., Fritsch, E. J. and Liederbach, J., 2014. Digital crime and digital terrorism. Prentice Hall Press.
- Levy, H. M., 2014. Capability-based computer systems. Digital Press.
- Kim, D. and Solomon, M. G., 2016. Fundamentals of information systems security. Jones & Bartlett Publishers.
- Peltier, T. R., 2016. Information Security Policies, Procedures, and Standards: guidelines for effective information security management. Auerbach Publications.
- Hsiao, D. K., Kerr, D. S. and Madnick, S. E., 2014. Computer security. Academic Press.
- Mendenhall, W. M., Sincich, T. L. and Boudreau, N. S., 2016. Statistics for Engineering and the Sciences, Student Solutions Manual. Chapman and Hall/CRC.
- Ahmed, M. and Hossain, M. A., 2014. Cloud computing and security issues in the cloud. International Journal of Network Security & Its Applications. 6(1). p.25.
- Comer, D. E., 2018. The Internet book: everything you need to know about computer networking and how the Internet works. Chapman and Hall/CRC.